30+ cyber security network diagram
Ad Are You Concerned with the Risk of a Security Breach in a Changing Landscape of Threats. Creation of well thought-out network security model will effectively help you in realization your networks security.

Access Programmer Consultants Access Database Relationship Diagram Database Design
Knapp Raj Samani in Applied Cyber Security and the Smart Grid 2013 Diagrams and Figures.

. Use PDF export for. Get the most powerful professional diagram software on the market. Learn Why Organizations Need to Address Risks Introduced During Transformation Efforts.
Ad Easily Find The Network Security Systems Youre Looking For w Our Comparison Grid. You can edit this template and create your own diagram. Creately diagrams can be exported and added to Word PPT powerpoint Excel Visio or any other document.
You can edit this template and create your own diagram. Creately diagrams can be exported and added to Word PPT powerpoint Excel Visio or any other document. Modernize your security strategy approach to survive the era of remote work and beyond.
See How HPE Can Help You Adopt a Zero Trust Framework to Close Gaps and Reduce Complexity. Use PDF export for. Prices and download plans.
Ad Complete your network diagram in minutes with automated network mapping from Auvik. At UKDataSecure we have the knowledge and experience required to support you in reviewing and updating your current network and data flow diagrams to support your. Ad Lucidcharts network diagram software is quick easy to use.
Ad Embracing a Zero Trust Security Model. Ad Explore Key Areas CISOs Should Focus on to be More Cyber Resilient with EY. A cloud and remote work security strategy.
Import Modify Visio. The network diagrams used throughout this book have also been intentionally. Ad Includes Networking Cisco LAN Rack Diagrams.
ConceptDraw PRO diagramming and vector drawing software extended. A Data Flow Diagram should. Ad Complete your network diagram in minutes with automated network mapping from Auvik.
Find the Best Network Security Systems That Will Help You Do What You Do Better. Sign in Sign up for FREE Prices and download plans. Lets break DFDs down a little bit.
Free trial up and running on your network in 30 minutes or less. Supplement an institutions understanding of information flow within and between network segments as well. These depictions are not to be construed as representing an engineering diagram for use in a production environment nor is segmentation the only tool to secure a network.
Free trial up and running on your network in 30 minutes or less.

Ex 99 2

Cyber Security Incident Response Cheat Sheet Behavior Analysis Cyber Security Analysis
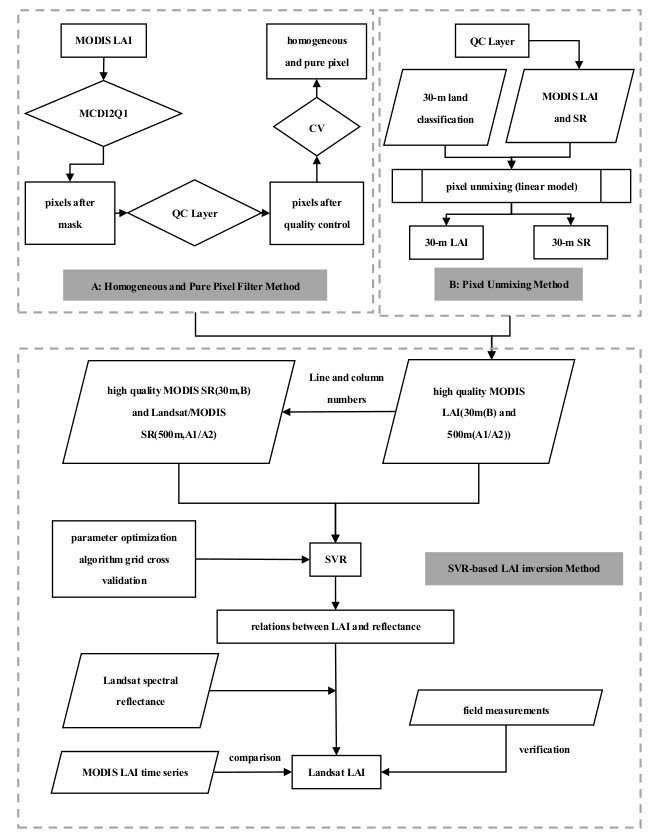
Remote Sensing Free Full Text The Retrieval Of 30 M Resolution Lai From Landsat Data By Combining Modis Products Html
25 Cyber Security Vulnerability Statistics And Facts Of 2022

Of Cybersecurity Passwords And Staying Safe Online Via Http Wpengine Com Unmasked Football 24 Cyber Security Abc 123

Cheat Sheets Packetlife Net Computer Programming Computer Technology Computer Network

Doug Madory Dougmadory Twitter

These Are The 5 Stages Of Growth Hacking Funnel That You Must Pass To Grow Your Business Entrepreneurship Sta Growth Marketing Growth Hacking Growth Medium

Secure And Intelligent Slice Resource Allocation In Vehicles Assisted Cyber Physical Systems Sciencedirect
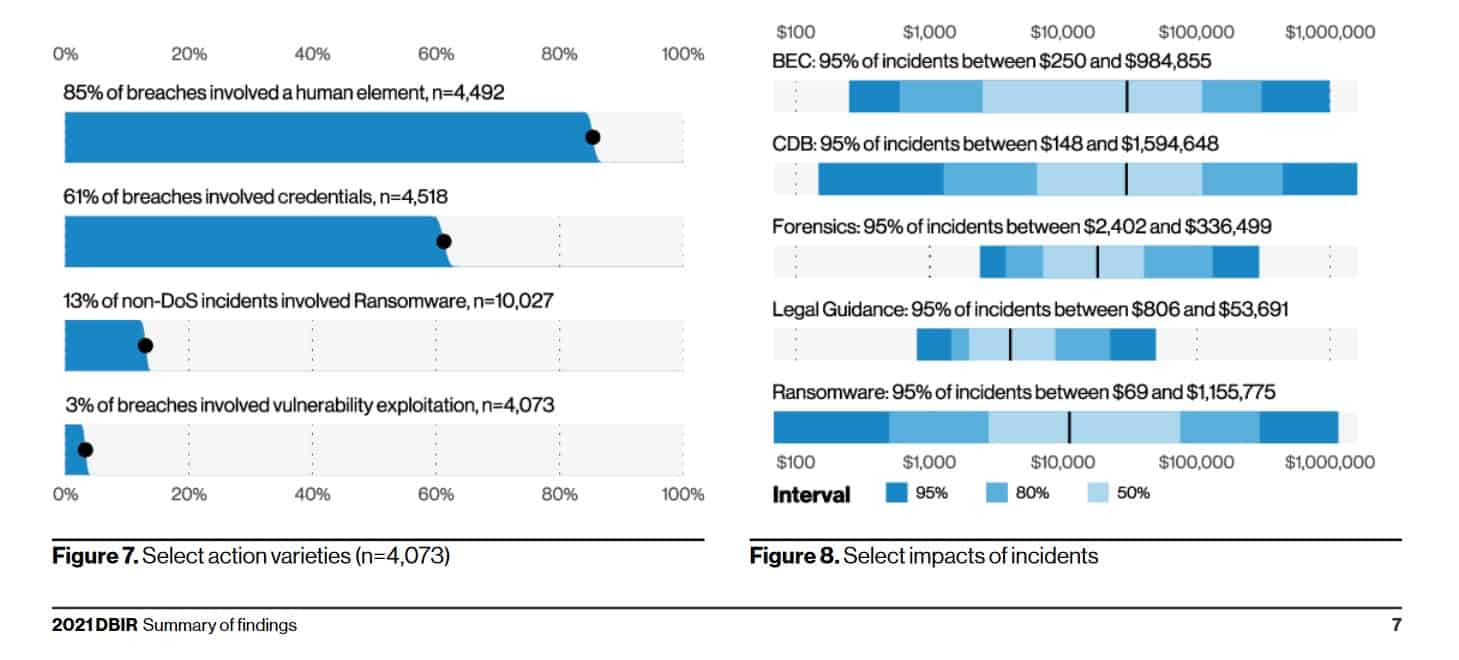
30 Data Breach Statistics And Facts Frequency Impact More

Access Programmer Consultants Access Database Relationship Diagram Database Design
30 Data Breach Statistics And Facts Frequency Impact More
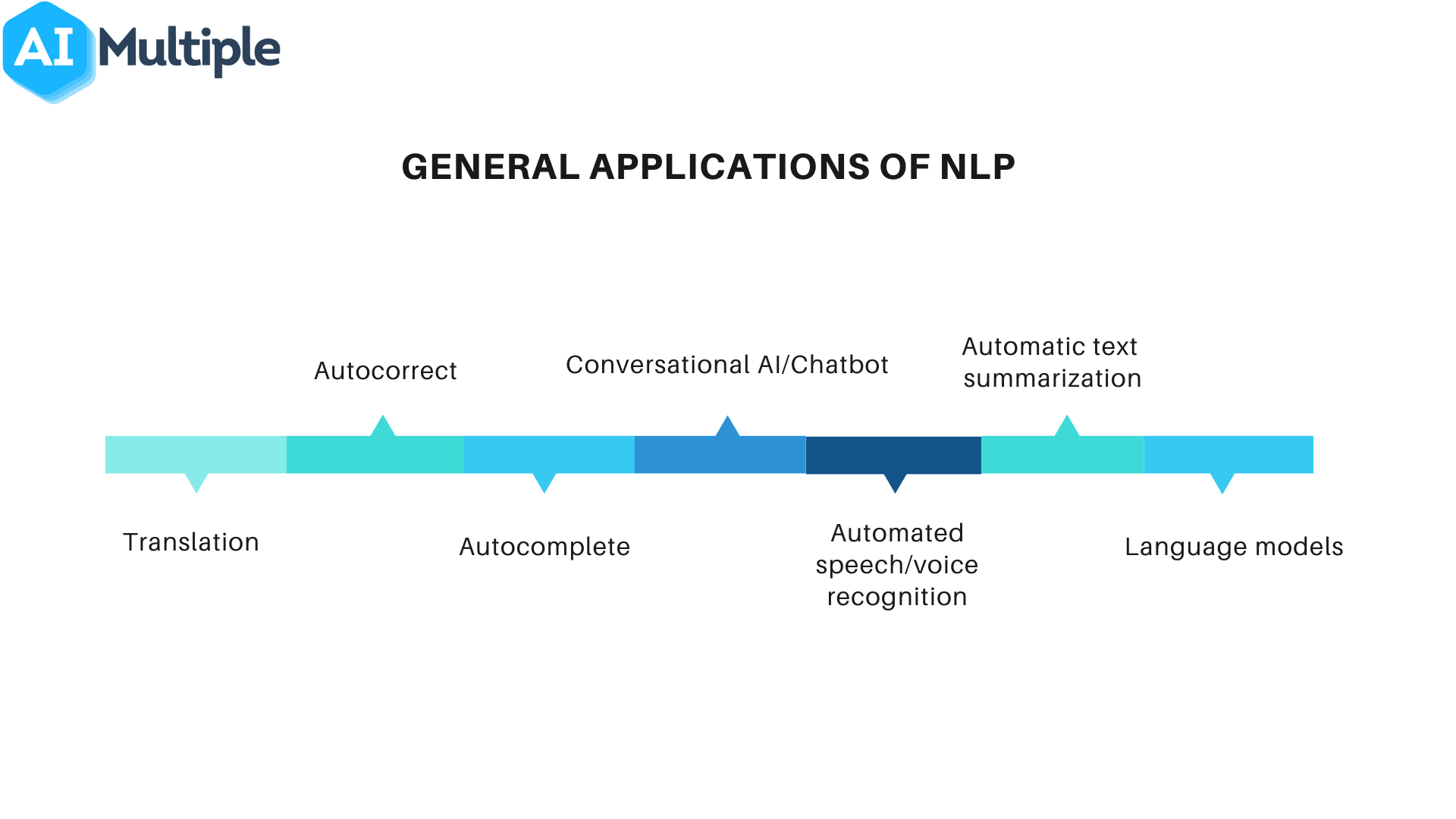
Comprehensive Guide To Top 30 Nlp Use Cases Applications
Enterprise Security

48 Devops Tools Ecosystem Linkedin Agile Software Development Ecosystems Data Science Learning

Seo Marketing Hub A Free Library Of Seo Resources Searchengineoptimization Digitalmarketing Seotips Seo Marketing Seo Software Marketing

What Is Network Security Introduction To Network Security Network Security Tutorial Simplilearn Youtube